Zero Trust security requires constant verification of every user, device, and transaction. The VIAVI Observer platform is a powerful tool to achieve this by offering extensive packet analysis and forensic capabilities. It ensures network visibility, supports compliance, and aids in detecting and investigating security threats.
Key takeaways:
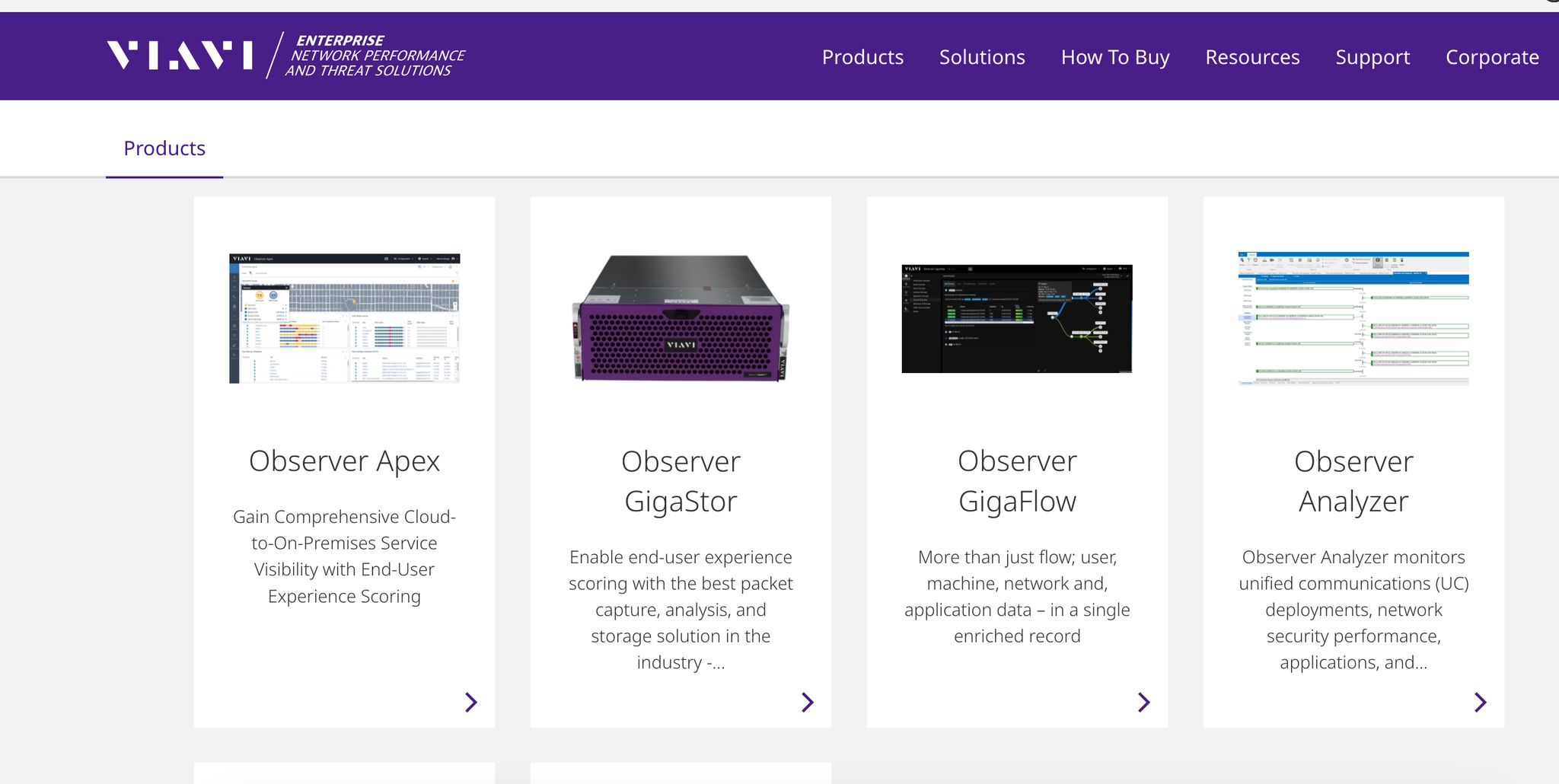
- VIAVI Observer tools: Includes GigaStor for packet retention, GigaFlow for enriched flow records, and Apex for insights – all essential for real-time and historical network analysis.
- Forensic capabilities: Helps identify breaches, trace anomalies, and meet regulatory standards with AES-256 encryption for data security.
- Deployment options: Offers flexibility across physical, virtual, and cloud environments, with scalable storage up to 5 petabytes.
- Real-world impact: Reduces breach detection times, supports compliance, and strengthens Zero Trust implementations.
For organizations in Canada, VIAVI Observer, combined with expert implementation partners like Telnet Networks, provides the tools needed to secure modern, complex networks effectively.
VIAVI Solutions Technology Overview
VIAVI Observer Platform Features
VIAVI Observer is designed to meet the rigorous demands of Zero Trust security and forensic analysis, offering a unified solution through its core components.
VIAVI Observer Architecture Overview
The VIAVI Observer platform is a powerful network performance monitoring and diagnostics solution, built on three key components: Observer Apex, GigaStor, and GigaFlow. Together, they provide a complete view of network activity by capturing, analyzing, and correlating data from multiple sources.
- Observer Apex acts as the brain of the platform, delivering insights into end-user experience using packets, metadata, and enriched flow data. It includes dashboards, application dependency mapping, and performance management tools, all integrated with forensic capabilities. By combining data from GigaStor and GigaFlow, Apex enhances troubleshooting and provides a deeper understanding of network environments.
- Observer GigaStor focuses on packet capture and retention, recording every network conversation for both real-time and historical analysis. It’s the backbone of forensic investigations, ensuring comprehensive packet records are secured with AES-256 encryption.
- Observer GigaFlow integrates network, infrastructure, and user data into detailed flow records. This provides insights into device types, connectivity patterns, traffic controls, and user behaviors across the enterprise.
"I prefer to consider the entire solution suite – GigaStor, along with GigaFlow and Apex – for comprehensive network visibility and monitoring." – Jeroen-Dubbelman, Director at Bitrate
The modular structure of the platform allows businesses to choose Observer Apex form factors that align with their IT needs, while also providing scalability to meet growing demands. This integrated system supports both real-time threat detection and in-depth historical analysis.
Real-Time and Historical Packet Capture
GigaStor is capable of capturing packets at speeds of up to 60 Gbps, supporting networks operating at 100 Gb. This ensures that even high-traffic environments maintain full packet visibility without any performance loss.
With storage capacities exceeding five petabytes, GigaStor enables organizations to retain extensive historical data, which is crucial for forensic investigations under a Zero Trust model. This capability allows security teams to analyze incidents that occurred weeks or even months earlier. Additionally, the GigaStor M variant increases write-to-storage performance by up to 40% when paired with standard GigaStor appliances.
The platform combines real-time analysis for immediate threat detection with historical packet capture for deep forensic investigations. By integrating with Observer Apex, it delivers actionable security intelligence. For organizations looking to plan storage requirements, the GigaStor calculator provides tailored recommendations.
Deployment Options for Canadian Enterprises
VIAVI Observer offers a range of deployment models to meet the diverse needs of Canadian enterprises, whether operating in physical, virtual, cloud, or hybrid environments. These options ensure the platform can be tailored to fit specific infrastructure requirements:
| GigaStor Form Factor | Storage Capacity |
|---|---|
| GigaStor Virtual | 256 GB – 64 TB |
| GigaStor Branch | 8 TB (SSD) |
| GigaStor Appliance (2U) | 24 TB – 1.2 PB |
| GigaStor Appliance (4U) | 192 TB – 1.2 PB |
| ObserverONE | 72 TB |
For high-traffic environments, physical appliances like the 2U and 4U models provide robust performance with storage ranging from 24 TB to 1.2 PB. Virtual deployments, on the other hand, offer flexibility for organizations with virtualized infrastructures, with storage options from 256 GB to 64 TB.
Cloud deployments are designed for hybrid and multi-cloud networks. Observer Apex is available as an Amazon Machine Image (AMI) for AWS, while GigaStor offers a cloud edition optimized for AWS environments. For remote offices, the GigaStor Branch solution provides 8 TB of SSD storage, enabling visibility without extensive local infrastructure.
"Applications are now distributed across private data centers, multiple public clouds, and edge locations, yet many companies fail to upgrade their network monitoring and management solutions to keep pace with these highly complex environments." – Bob Laliberte, Principal Analyst, Enterprise Strategy Group
Observer Analyzer adds further flexibility, as it can be deployed on engineers’ laptops for portable analysis or set up centrally for continuous monitoring and alerts. This supports the ongoing monitoring required in a Zero Trust framework. To ensure smooth implementation, VIAVI Solutions Consulting offers services ranging from quick setup to comprehensive on-site deployment, helping US enterprises successfully integrate Observer into their existing networks.
Historical Packet Capture for Forensics and Compliance
Historical packet capture takes network security to the next level by recording every transaction on the network. This approach is especially crucial in Zero Trust environments, where every interaction must be verified and documented.
How Historical Packet Capture Works
The VIAVI Observer operates as a continuous monitoring tool, keeping an eye on all network connections, communications, and transactions around the clock. It captures every packet moving through the network, storing it with precise timestamps and location details for future reference.
With a speed of up to 60 Gbps, the system ensures no packet is lost, even during periods of heavy traffic. GigaStor appliances are designed to handle five years of nonstop, full-capacity packet capture without any drop in performance. This means your security team has access to a complete record of network activity, even during peak usage times.
Observer’s wire-data capture provides a detailed view of network transactions. By analyzing NAT/PAT data from devices that translate addresses, it creates a comprehensive end-to-end picture of each transaction. This allows IT teams to pinpoint specific events or anomalies from the past, identifying exactly who was affected and when, where, and how the incident occurred. The integration of packet and flow data makes the information easy to interpret and act upon.
This level of visibility lays the groundwork for thorough forensic investigations and helps organizations meet regulatory requirements.
Forensics and Compliance Use Cases
The captured data enables precise forensic investigations and helps organizations comply with strict regulatory standards. During incidents, Observer facilitates swift analysis, quickly identifying entry points, dwell times, lateral movements, and accessed data. This is critical, considering the average cost of a data breach exceeds $4 million, and it typically takes 277 days to contain one.
Take the June 2019 NASA JPL breach as an example. A malicious actor exploited an unauthorized Raspberry Pi device to infiltrate the NASA JPL network in Pasadena, CA. Over 10 months, the hacker exfiltrated 500 MB of data from 23 files, including sensitive information governed by International Traffic in Arms Regulations related to the Mars Science Laboratory mission. With flow-based analysis and enriched-flow records, VIAVI could have helped identify connected devices and communications across the network.
Observer also tracks lateral movements, helping security teams gauge the extent and severity of breaches while gaining insights into the attacker’s methods. This knowledge is invaluable for strengthening defenses against future threats.
To meet compliance requirements, Observer ensures AES-256 encryption for data at rest, providing long-term visibility and security. This allows organizations to demonstrate accountability by presenting complete network activity records during audits. In fact, 91% of IT professionals agree that visibility into endpoints, servers, and other network components significantly improves security monitoring.
"With the Observer Platform, the ability to get an expert analysis relatively quickly is the best benefit. The capture is constantly running, so we can analyze any time we like without setting up extra equipment." – Landrin Long, State of Nevada Department of Information Technology
Organizations that integrate wire data into their cybersecurity tools see faster breach detection and response times, reducing both the impact on operations and the cost of remediation.
Data Storage and Indexing for Large Networks
Handling the enormous amounts of data generated by network activity requires advanced storage and analysis tools. VIAVI Observer supports scalable storage exceeding five petabytes, with deployment options tailored to fit different organizational needs. It continuously collects enriched-flow records, including timestamps and location data, ensuring access to forensic details over extended periods.
The platform offers tiered storage options, allowing frequently accessed data to reside on high-speed storage while archiving older data more cost-effectively. Enhanced write-to-storage capabilities ensure complete packet capture without affecting network performance, even in high-traffic environments. For organizations planning their storage needs, VIAVI provides a GigaStor calculator to help estimate the required storage size based on traffic and retention goals.
"The options that are available and the power of the product are amazing. We’ve solved more problems quicker with Observer than any other analyzing software we’ve had." – Landrin Long, State of Nevada Department of Information Technology
Zero Trust Implementation with VIAVI Observer
Zero Trust thrives on the principle of constant verification – every user, device, and transaction must pass scrutiny. VIAVI Observer strengthens this approach by leveraging its expertise in packet capture and forensic analysis. It provides the visibility and insights needed to implement and sustain Zero Trust security policies across enterprise networks.
Complete Network Visibility
A lack of network visibility is a major issue for most organizations, with fewer than 1% expressing satisfaction in this area – even as enterprise applications increasingly move to the cloud. This visibility gap creates vulnerabilities that attackers can exploit. VIAVI Observer eliminates these blind spots by integrating multiple data sources into a unified platform.
By combining packet capture with end-user experience (EUE) scoring, Observer offers a complete view of network activity. It transforms raw packet and flow data into actionable visualizations, tracking communications across the entire network infrastructure. This capability is especially valuable for hybrid environments and cloud migration assessments, addressing one of the most significant challenges for NetOps teams: problem domain isolation.
"Our focus continues to be not on delivering more KPIs, but delivering more clarity, actionable information, and business value." – Chris Labac, Vice President and General Manager, Network Performance and Threat Solutions, VIAVI
This comprehensive visibility lays the groundwork for real-time analysis of user and device behavior.
User and Device Behavior Analysis
To uphold Zero Trust principles, it’s essential to understand typical behavior patterns and detect deviations that may indicate threats. VIAVI Observer uses packet-level data to analyze user and device behavior, helping identify anomalies that could signal security breaches. The platform builds detailed profiles of network activity, establishing baselines for what constitutes normal behavior.
Observer’s traffic profiling compares current activity with historical patterns, creating device profiles that make it easier to spot unauthorized access attempts or unusual communications before they escalate. Additionally, the platform generates enriched flow records, offering insights into relationships between users, IP addresses, MAC addresses, and application usage. By integrating with Active Directory, Observer adds critical context about who is accessing specific resources and when, a key element for continuous verification in a Zero Trust model.
The platform also monitors lateral movements within the network, alerting IT teams to unauthorized access attempts. This is especially important as it can take an average of 277 days to contain a data breach. These insights enable security teams to act swiftly and effectively, reinforcing network defenses.
Network Segmentation and Policy Validation
Network segmentation and Zero Trust complement each other by creating layered security defenses. Segmentation isolates sensitive assets, limiting the scope of potential breaches, while Zero Trust ensures continuous verification of all network entities. VIAVI Observer provides the visibility needed to confirm that both strategies are functioning as intended.
Observer supports the "Verify usage" aspect of the Continuous Adaptive Risk & Trust Assessment (CARTA) framework by monitoring compliance and identifying exceptions. It offers detailed insights into both east-west and north-south traffic, helping teams detect potential policy violations or suspicious activities.
The platform’s dependency mapping feature allows IT teams to validate user access to devices and services. Its IP Viewer tool compiles layer 2 and 3 data into interactive visualizations, highlighting relationships between users, IP/MAC addresses, and application usage. Combined with automated profiling in Observer GigaFlow, which flags unauthorized access attempts, these tools help enforce effective network segmentation policies.
With Gartner reporting a 60% annual growth rate for Zero Trust Network Access (ZTNA), organizations require tools capable of adapting to evolving networks and threats. VIAVI Observer delivers the forensic analysis and real-time monitoring necessary to ensure Zero Trust policies remain effective in an ever-changing landscape.
sbb-itb-f59d864
Optimizing Network Performance and Security with Observer
Telnet Networks leverages Observer’s advanced capabilities to ensure continuous, compliant monitoring. Observer GigaStor captures packets at speeds of 60 Gbps, processes 14.3 million packets per second, and offers scalable storage exceeding a petabyte.
Independent tests confirm that GigaStor achieves 100% packet capture, enabling precise analysis and metadata generation. The platform supports uninterrupted, five-year, full-duty-cycle packet capture without data loss, ensuring the long-term visibility needed for thorough forensic investigations.
Observer’s 3D capabilities enhance Zero Trust Network Access (ZTNA) by monitoring compliance, identifying exceptions, and mitigating risks. With features like on-demand application dependency mapping, IP Viewer functionality, and advanced profiling, organizations can validate their Zero Trust implementations, track user access, and pinpoint security gaps.
"Observer 18 empowers stakeholders from business leaders to level 3 support with customizable, streamlined workflows and intuitive visualizations, based on the most complete data set available. When they take control, they can guarantee that both work and learning can happen, wherever it needs to happen." – Charles Thompson, Senior Director, Enterprise and Cloud at VIAVI
"Whether ensuring optimal end user experience or addressing security threats, maintaining IT service health begins with complete visibility into network traffic." – Kevin Tolly, Founder of The Tolly Group
VIAVI Observer’s packet capture capabilities are particularly valuable for compliance reporting and regulatory investigations in industries like finance, healthcare, and legal. Its advanced monitoring extends to AWS and Azure cloud platforms, ensuring hybrid and multi-cloud environments maintain the same security and compliance standards as on-premises systems.
For US enterprises adopting Zero Trust architectures, Telnet Networks’ integration of VIAVI Observer offers the visibility and forensic tools essential for maintaining compliance, detecting anomalies, and addressing today’s sophisticated security threats.
Conclusion: Historical Packet Capture Value in Zero Trust
VIAVI Observer Benefits for Zero Trust
Historical packet capture plays a vital role in making Zero Trust strategies actionable by offering a complete record of network events. This level of visibility is essential for maintaining compliance with Zero Trust principles, which demand that no user or device is trusted without verification. By providing comprehensive monitoring, Observer directly supports the core tenet of Zero Trust: "never trust, always verify."
Observer combines flow data with packet capture to eliminate blind spots and accelerate incident response. With support for decoding over 740 primary protocols, it empowers organizations to analyze virtually any network communication within their Zero Trust framework. This granular visibility is critical for enforcing the stringent security standards that Zero Trust requires.
Compliance is another area where Observer excels. Its GigaStor tool offers AES-256 encryption for data at rest and generates court-admissible packet evidence, helping organizations meet even the most rigorous regulatory requirements while maintaining detailed audit trails. This capability is especially important given the financial and operational impact of data breaches, which cost an average of $4 million and take 277 days to contain.
These technical strengths provide a solid foundation for expert implementation by trusted partners like Telnet Networks.
Telnet Networks Support for US Enterprises
Telnet Networks builds on the strengths of VIAVI Observer to address the unique regulatory and operational challenges faced by US enterprises. With over 25 years of experience, Telnet Networks specializes in guiding organizations through the complexities of Zero Trust implementation. Their expertise spans network performance management, security tools, and compliance – key areas for modern businesses.
Using Observer’s advanced capabilities, Telnet Networks helps US businesses navigate varying regulatory frameworks across states and industries. Their tailored approach ensures that Observer deployments meet both technical and compliance needs, providing organizations with the tools to achieve Zero Trust maturity.
By integrating Observer’s GigaStor and GigaFlow tools, Telnet Networks delivers comprehensive monitoring solutions that enable continuous packet capture for threat investigations and network audits. This is particularly valuable given that only 36% of CISOs have started implementing Zero Trust components.
"There can be no Zero Trust without visibility into what’s happening inside networks" – Heath Mullins, Senior Analyst at Forrester
Telnet Networks ensures that US enterprises can fully leverage Observer’s continuous capture capabilities to establish the historical visibility needed for effective Zero Trust architectures. Their support extends beyond deployment, focusing on ongoing optimization to help organizations validate policies and identify vulnerabilities before they escalate into costly breaches.
The partnership between VIAVI Observer’s technical solutions and Telnet Networks’ implementation expertise offers US enterprises a clear path to achieving the network visibility and forensic analysis critical for Zero Trust success.
FAQs
How does the VIAVI Observer platform support Zero Trust Network implementation and enhance security?
The VIAVI Observer platform plays a key role in strengthening Zero Trust Network Access (ZTNA) strategies by offering detailed network visibility and powerful monitoring tools. These tools empower organizations to spot risks, stay compliant, and maintain strong security measures.
Here’s what makes it stand out:
- Application Dependency Mapping: Ensures that only authorized users and devices can access specific services.
- IP Viewer: Provides a clear view of user, IP address, and application connections, making it easier to detect policy violations.
- Observer GigaFlow Profiling: Monitors network activity in real time to quickly identify unauthorized access or unusual behavior.
By delivering accurate monitoring and rapid anomaly detection, VIAVI Observer helps organizations take a proactive approach to risk management, reinforcing their Zero Trust security framework.
How does historical packet capture support forensic investigations and help meet regulatory compliance requirements?
Historical packet capture serves as a detailed archive of past network activity, giving security teams the ability to retrace steps, detect breaches, and spot malicious behavior. This kind of visibility is crucial for forensic investigations, as it helps pinpoint the exact cause of incidents and bolsters overall security defenses.
Beyond its role in incident analysis, keeping thorough packet logs also aids in regulatory compliance. These records can act as proof of network activity during audits or investigations, helping organizations meet legal and industry requirements. By combining deeper security insights with compliance support, historical packet capture has become an essential component of modern cybersecurity practices.
What deployment options does VIAVI Observer provide, and how can it be customized to meet different network environments?
VIAVI Observer provides a range of deployment options to match different network setups. Whether you’re working in the cloud or managing a hybrid infrastructure, this platform has you covered. It offers virtual machine images for cloud-based applications and scalable solutions designed to handle the complexities of hybrid environments.
You can also customize the platform to meet your organization’s specific requirements. With features like customizable dashboards, support for Azure and AWS flow logs, and real-time visibility across virtual, cloud, and remote environments, VIAVI Observer integrates smoothly into your existing network. This not only boosts performance but also strengthens your network’s security.






