While security experts may disagree on exactly how to secure a network, one thing they all agree on is that you cannot defend against what you cannot see. In other words, network visibility IS network security.
Visibility needs to be the starting the point. After that, you can implement whatever appliances, processes, and configurations you need to finish off the security architecture. By adopting this strategy, IT will acquire an even better insight and understanding of the network and application performance to maximize security defenses and breach remediation.
For instance, early detection of breaches using application data reduces the loss of personally identifiable information (PII) and reduces breach costs. Specifically, application level information can be used to expose indicators of compromise, provide geolocation of attack vectors, and combat secure sockets layer (SSL) encrypted threats.
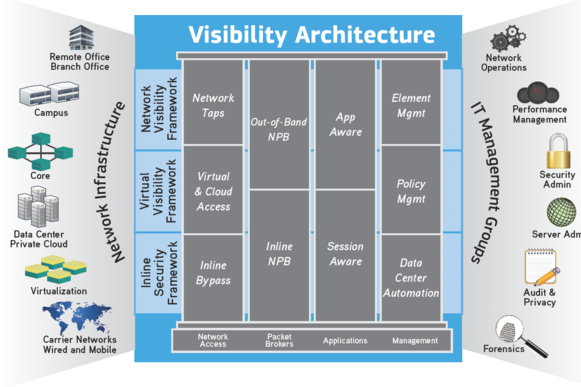
You might be asking, what is a visibility architecture?
A visibility architecture is nothing more than an end-to-end infrastructure which enables physical and virtual network, application, and security visibility. This includes taps, bypass switches, packet brokers, security and monitoring tools, and application-level solutions.
A core benefit of application intelligence is the ability to use application data filtering to improve security and monitoring tool efficiencies. Delivering the right information is critical because as we all know, garbage in results in garbage out.
EXPOSING INDICATORS OF COMPROMISE (IOC)
The main purpose of investigating indicators of compromise for security attacks is so that you can discover and remediate breaches faster. Security breaches almost always leave behind some indication of the intrusion, whether it is malware, suspicious activity, some sign of other exploit, or the IP addresses of the malware controller.
Despite this, most victimized companies don’t discover security breaches themselves. Approximately 75% have to be informed by law enforcement and 3rd parties (customers, suppliers, business partners, etc.) that they have been breached. In other words, the company had no idea the breach had happened.
To make matters worse, the average time for the breach detection was 168 days!
To thwart these security attacks, you need the ability to detect application signatures and monitor your network so that you know what is, and what is not, happening on your network. This allows you to see rogue applications running on your network along with visible footprints that hackers leave as they travel through your systems and networks. The key is to look at a macroscopic, or application view, of the network for IOC.
For instance, suppose there is a foreign actor in Eastern Europe (or other area of the world) that has gained access to your network. Using application data and geo-location information, you would easily be able to see that someone in Eastern Europe is transferring files off of the network from an FTP server in Dallas, Texas back to an address in Eastern Europe.
Is this an issue? It depends upon whether you have authorized users in that location or not. If not, it’s probably a problem.
Due to application intelligence, you now know that the activity is happening. The rest is up to you to decide if this is an indicator of compromise for your network or not.
Thank you to Keith Bromley and APM Digest for the article.