In today's rapidly evolving cyber threat landscape, the emergence of AI-generated attacks has posed significant challenges to traditional Network Detection and Response (NDR) solutions. These sophisticated threats can outpace conventional security measures, leaving organizations vulnerable. Recognizing this pressing issue, CySight CEO Rafi Sabel re...
-
Call Us:1.800.561.4019
Newsletter
For a Free Quote...
Latest Blog Posts
Blog Categories
Telnet Networks News
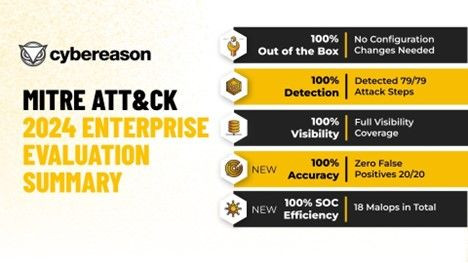
Telnet Networks' partner, Cybereason, has once again solidified its position as a leader in this domain by achieving perfect scores in the 2024 MITRE ATT&CK® Enterprise Evaluation. This accomplishment builds on excellent showings in the 2023 and 2022 editions of the evaluation underscores Cybereason's commitment to excellence and reaffirms Teln...
Network visibility and security are two essential aspects of managing modern networks. Visibility focuses on monitoring and understanding traffic, devices, and user behaviour, while security actively protects networks from threats like malware and breaches. Both are critical, but they serve different purposes and complement each other to build stro...
Network Detection and Response (NDR) is a cybersecurity approach that focuses on identifying and mitigating malicious activities in real-time. So, what is Network Detection and Response (NDR)? Network Detection and Response uses non-signature-based techniques (as opposed to the signatures used by anti-virus/anti-malware) such as machine learning to...
Canada's healthcare sector is undergoing a digital transformation, with hospitals increasingly relying on connected medical devices (CMDs) like infusion pumps and imaging equipment to deliver better patient outcomes and optimize staff efficiency. While this shift improves diagnostic and treatment capabilities, it also introduces new cybersecurity v...
Network visibility is crucial for strengthening Operational Technology (OT) security, which protects critical infrastructure and industrial systems from cyber threats. Here's how improved network visibility addresses key OT security challenges: Early Threat Detection Network visibility tools offer comprehensive monitoring of all network traffic, in...
Is your OT network secure enough? As the reliance on interconnected systems for critical operations grows, the security of Operational Technology (OT) networks becomes increasingly crucial. Traditional monitoring methods like SPAN ports often fall short, leaving your network exposed to vulnerabilities.Discover how Cubro network TAPs can be the corn...
Enhancing Impelix IMPACT Next-Generation SIEM with Network Flow Data from Cubro A comprehensive understanding of cybersecurity and organizational risk has become a requirement for ongoing stability and success for every organization. Join Impelix and Cubro to explore the seamless integration of Impelix's cutting-edge SecOps Platform with Cubro's ne...
By Filip Cerny of Flowmon Network Detection and Response (NDR) is a cybersecurity approach that focuses on identifying and mitigating malicious activities in real-time. NDR is an indispensable piece of an overall security operation strategy. So, what is Network Detection and Response (NDR)? Network Detection and Response uses non-signature-based te...
5G has introduced a number of improvements in security compared to 4G. 5G standards development has adopted 'Secure by Design' principles, using for example Mutual Authentication and acknowledging that all links could be tapped, but making sure that the encrypted information is worthless when intercepted. Security is a wide topic and has different ...
As organizations move towards higher-speed networks like 100/400G, they often encounter unexpected hurdles when it comes to security monitoring. The need for faster data transmission clashes with the limitations of existing tools, leaving them ineffective and struggling to keep up. In this blog, we will explore the challenges faced in security moni...
Written by Maranda Cigna, Vice President of Product Marketing at Cybereason Fresh off the press: the results of the 2023 MITRE Engenuity ATT&CK® Evaluations: Enterprise have been published, putting 30 security solutions to the test in real world scenarios that mimic the Turla threat actor. As is customary, many vendors have been in a frenz...
Keysight has released its 2023 Security Report. This report explores the key threats in 2022 and what you can expect in 2023. The key take away discussed in the report. 1. Ransomware will be a constant threat that must be addressed ahead of time by IT security departments Ransomware security attack successes are an indicator of a weakness in m...
A recent Enterprise Management Associates survey (Network Visibility Architecture for the Hybrid, Multi-Cloud Enterprise) found that 46% of IT professionals admitted that their migration to a cloud-based network created blind spots. Furthermore, the number of blind spots increased directly with the increase in the number of cloud networks deployed,...
Anyone in network security knows that it is a complicated and involved process. The clear goal is to prevent security breaches. How do you go about that though? There are so many schools of thought, methods, and configurations. Here are just a few examples: Cyber range trainingCyber resilience Defense in depthEncryptionEndpoint securityFirewallsInl...
Network monitoring can be described in many ways, but very often it is defined in the following way: 'Network management is the process of configuring, monitoring and maintaining a reliable network ensuring connectivity between devices and the people or software applications.' Several frameworks have been developed around network monitoring, for ex...
Cubro Network Visibility commissioned Tolly, a leading global provider of third-party validation services for vendors of IT products, components and services, to evaluate the usability, storage efficiency and approach to data structure used in Custos. Tests were run by evaluating a live network simultaneously using Cubro Custos and legacy NetFlow/ ...
Every Network Has a Security Vulnerability – Where is Yours? One of the top questions on the minds of network security personnel is "how do I reduce my security risk?" Even for smaller organizations, this is important because every network has a weakness. But do you know where you are the most vulnerable? Wouldn't you like to fix the problem now, b...
By Gregory Copeland, Director - Technical Alliances at Keysight Technologies Cybersecurity is rightfully a top concern for Enterprises and getting more so with all the high-profile breaches making the news. Leaders don't want their company making the news having fallen victim to a massive ransomware attack or denial of service. Consequently, ...
Every network has a security vulnerability. Vulnerabilities obviously lead to threats. Do you know where your vulnerabilities and any hidden threats are located? With major security breaches happening every year to businesses and government agencies of every type, don't you want to find (and fix) your network BEFORE a hacker finds and exploits the ...